Stop the Network-Based Application Recognition Nonsense
One of my readers sent me an interesting update on the post-QUIC round of NBAR whack-a-mole (TL&DR: everything is better with Bluetooth AI):
So far, so good. However, whenever there’s a change, there’s an opportunity for marketing FUD, coming from the usual direction.
Presentation: Introduction to netlab
Yesterday, I had an Intro to netlab presentation at the wonderful RIPE SEE meeting in Athens. The presentation is already online; I will update this blog post once the recordings are published.
Repost: Campus-Wide Wireless Roaming with EVPN
As a response to my LISP vs EVPN: Mobility in Campus Networks blog post, Route Abel provided interesting real-life details of a large-scale campus wireless testing using EVPN and VXLAN tunnels to a central aggregation point (slightly edited):
I was arguing for VxLAN EVPN with some of my peers, but I had no direct hands-on knowledge of how it would actually perform and very limited ability to lab it on hardware. My client was considering deploying Campus VxLAN, and they have one of the largest campuses in North America.
Worth Reading: Data Protection for Dummies
Another lovely must-read rant from the cranky security professional.
TL&DR: Data protection requirements like PCI-DSS aren’t there to make companies more secure but to make it too expensive for them to hoard excessive customer data (see also: GDPR).
FRRouting Loopback Interfaces and OSPF Costs
TL&DR: FRRouting advertises the IP prefix on the lo loopback interface with zero cost.
Let’s start with the background story. When we added FRRouting containers support to netlab, someone decided to use lo0 as the loopback interface name. That device doesn’t exist in a typical Linux container, but it’s not hard to add it:
$ ip link add lo0 type dummy
$ ip link set dev lo0 up
Unintended Consequences of IPv6 SLAAC
One of my friends is running a large IPv6 network and has already experienced a shortage of IPv6 neighbor cache on some of his switches. Digging deeper into the root causes, he discovered:
In my larger environments, I see significant neighbor table cache entries, especially on network segments with hosts that make many long-term connections. These hosts have 10 to 20 addresses that maintain state over days or weeks to accomplish their processes.
What’s going on? A perfect storm of numerous unrelated annoyances:
Explore: Why No IPv6? (IPv6 SaaS)
Lasse Haugen had enough of the never-ending “we can’t possibly deploy IPv6” excuses and decided to start the IPv6 Shame-as-a-Service website, documenting top websites that still don’t offer IPv6 connectivity.
His list includes well-known entries like twitter.com, azure.com, and github.com plus a few unexpected ones. I find cloudflare.net not having an AAAA DNS record truly hilarious. Someone within the company that flawlessly provided my website with IPv6 connectivity for years obviously still has some reservations about their own dogfood ;)
Public Videos: Kubernetes Ingress

All the Kubernetes Ingress videos from the Kubernetes Networking Deep Dive webinar with Stuart Charlton are now public. Enjoy!
LISP vs EVPN: Mobility in Campus Networks
I decided not to get involved in the EVPN-versus-LISP debates anymore; I’d written everything I had to say about LISP. However, I still get annoyed when experienced networking engineers fall for marketing gimmicks disguised as technical arguments. Here’s a recent one:

Stateful Firewall Cluster High Availability Theater
Dmitry Perets wrote an excellent description of how typical firewall cluster solutions implement control-plane high availability, in particular, the routing protocol Graceful Restart feature (slightly edited):
Most of the HA clustering solutions for stateful firewalls that I know implement a single-brain model, where the entire cluster is seen by the outside network as a single node. The node that is currently primary runs the control plane (hence, I call it single-brain). Sessions and the forwarding plane are synchronized between the nodes.
SR/MPLS Security Framework
A long-time friend sent me this question:
I would like your advice or a reference to a security framework I must consider when building a green field backbone in SR/MPLS.
Before going into the details, keep in mind that the core SR/MPLS functionality is not much different than the traditional MPLS:
netlab 1.8.1: VRF OSPFv3, Integration Tests
netlab release 1.8.1 added a interesting few features, including:
- OSPFv3 in VRFs, implemented on Arista EOS, Cisco IOS, Cisco IOS-XE, FRR, and Junos (vMX, vPTX, vSRX).
- EBGP sessions over IPv4 unnumbered and IPv6 LLA interfaces on Arista EOS
- Cisco IOS XRd container support
- Retry tests until the timeout functionality in netlab validate.
This time, most of the work was done behind the scenes1.
Worth Reading: Cybersecurity Is Broken
Another cybersecurity rant worth reading: cybersecurity is broken due to lack of consequences.
Bonus point: pointer to RFC 602 written in December 1973.
Why Are We Using EVPN Instead of SPB or TRILL?
Dan left an interesting comment on one of my previous blog posts:
It strikes me that the entire industry lost out when we didn’t do SPB or TRILL. Specifically, I like how Avaya did SPB.
Oh, we did TRILL. Three vendors did it in different proprietary ways, but I’m digressing.
BGP Challenge: Build BGP-Free MPLS Core Network
Here’s another challenge for BGP aficionados: build an MPLS-based transit network without BGP running on core routers.
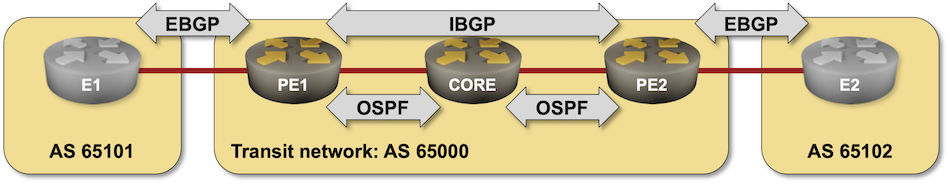
That should be an easy task if you configured MPLS in the past, so try to spice it up a bit:
- Use SR/MPLS instead of LDP
- Do it on a platform you’re not familiar with (hint: Arista vEOS is a bit different from Cisco IOS)
- Try to get it running on FRR containers.
